 Ransomware has been on the rise over the last six months.
Ransomware has been on the rise over the last six months.
I have noticed a huge increase in the number of inquiries from people who have been infected with viruses that have encrypted the data on their Hard Drives.
This article gives you some options for decrypting your data without paying the ransom.
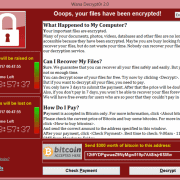
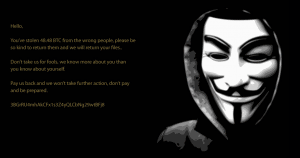
These viruses, collectively know as “Ransomware”, encrypt your files (Documents, Photos and other files) and then attempt to extort you by requesting payment to unlock those files.
Up until recent times, my advice has been that there is little choice other than to wipe the Hard Drive and reinstall Windows and software, and if available, restore a backup of your files.
Recently however, a couple of other options have come to my attention.
Ransomware Decryption Tools
The first comes from AVG. They have released six Decryption Tools that (if you’re lucky) may help with decrypting your data.
The six methods of encrytion that these tools target are:
- Apocalypse,
- BadBlock,
- Crypt888,
- Legion,
- SZFLocker, and
- TeslaCrypt.
You can access these decryption tools here.
The second option is in the form of other decryption tools from a website setup by Europol.
These tools attempt to decrypt the following:
CoinVault
The National High Tech Crime Unit (NHTCU) of the Netherlands’ police, the Netherlands’ National Prosecutors Office and Kaspersky Lab, have been working together to fight the CoinVault and Bitcryptor ransomware campaigns.
RannohDecryptor
The RannohDecryptor tool is intended to be used to decrypt files encrypted by:
- Rannoh,
- AutoIt,
- Fury,
- Crybola,
- Cryakl, and
- CryptXXX versions 1 and 2 (files encrypted by Trojan-Ransom.Win32.CryptXXX version 3 are detected, but not decrypted).
RakhniDecryptor
The RakhniDecryptor tool is intended to be used to decrypt files encrypted by:
- Rakhni,
- Agent.iih,
- Aura,
- Autoit,
- Pletor,
- Rotor,
- Lamer,
- Lortok,
- Cryptokluchen,
- Democry, and
- Bitman (TeslaCrypt) version 3 and 4.
ShadeDecryptor
ShadeDecryptor can decrypt files with the following extensions: .xtbl, .ytbl, .breaking_bad, .heisenberg.
You can access these decryption tools here.
Prevention is better than cure
Of course it goes without saying that prevention is better than cure.
The reason you will get one of these viruses normally stems from opening an attachment in a Phishing email.
A Phishing email is one that is constructed to look like it comes from a reputable source.
Examples are:
- The Bank;
- An Energy supplier. ie. AGL, Origin etc;
- Australia Post;
- A Courier. ie DHL, Toll etc.
Also, the prevailing advice is never pay the ransom.
By paying cybercriminals, you only confirm that ransomware works, but more importantly, there is no guarantee that you will receive the encryption key you need to unlock your data.
Spotty Dog Computer Services can remove Ransomware from your Computer.










 I recently read a quote that was meant to apply to Businesses, but equally applies to anyone online. And it went like this:
I recently read a quote that was meant to apply to Businesses, but equally applies to anyone online. And it went like this: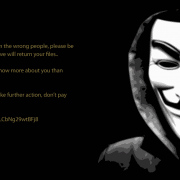
 Ransomware has been on the rise over the last six months.
Ransomware has been on the rise over the last six months.